A technology correspondent recently detailed the successful circumvention of a forty-year-old hardware security dongle that was necessary to operate a highly legacy accounting software package. This software, written in the Report Program Generator (RPG) language, was still in use by an accounting firm running on a Windows 98 system within a DOS console environment.
This required hardware key, connected via the parallel port, was a common method for protecting proprietary enterprise software during that era, according to the report published on dmitrybrant.com. Clues on the worn device suggested an origin with Software Security Inc. of Stamford, CT, a firm known for exhibiting security wares at SIGGRAPH conferences in the early 1990s.
The initial step involved creating a disk image of the Windows 98 PC to analyze the system and attempt data migration to modern tools. Analysis of the disk image revealed the RPG II compiler, source code for the accounting suite, and associated DOS batch orchestration files.
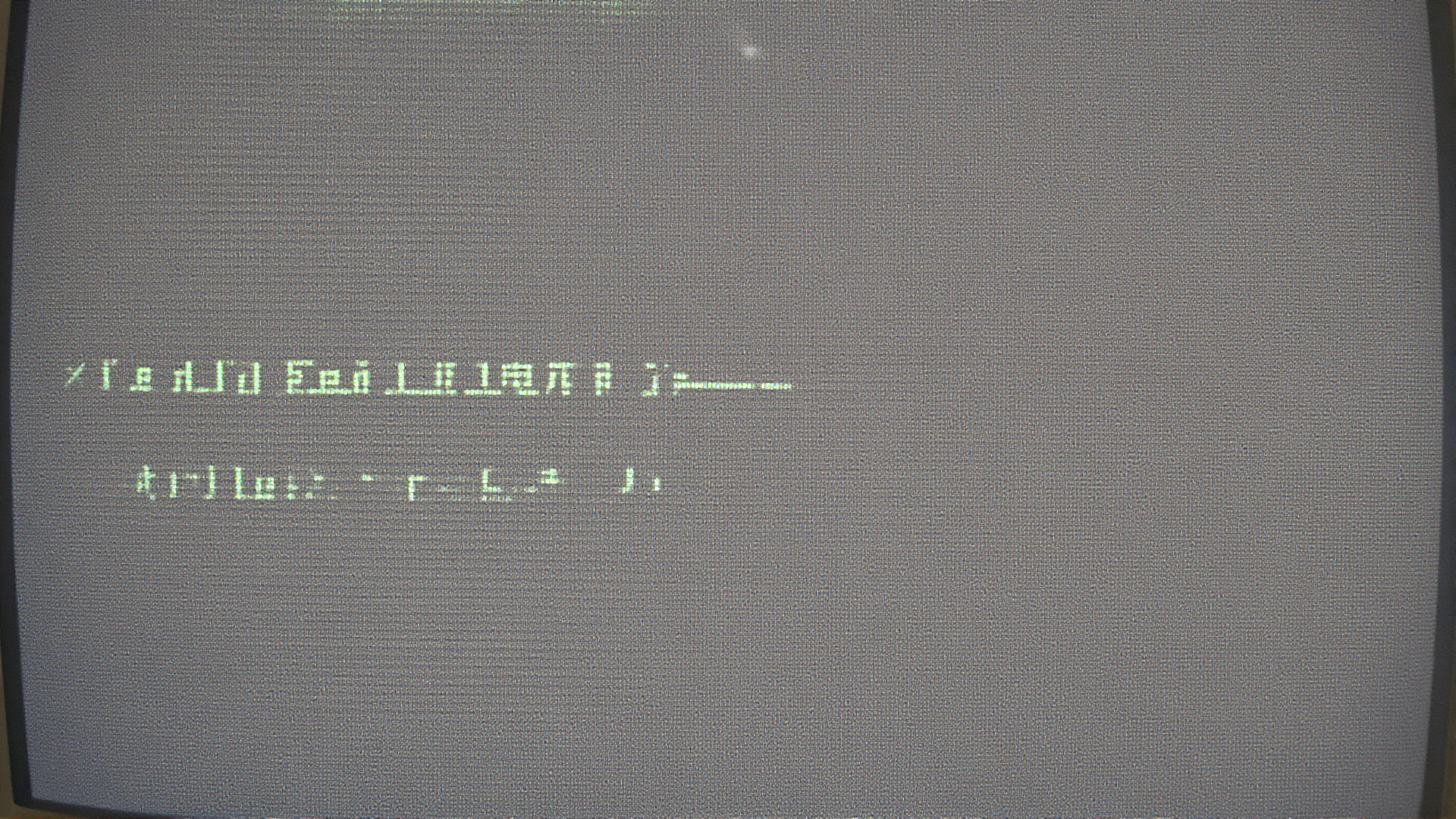
Crucially, the researcher determined that the RPG compiler itself enforced the copy protection, subsequently injecting the same logic into all compiled executables. When attempting to run the compiler without the dongle, the program would pause for several seconds while querying the parallel port before displaying an error message.
Using the Reko disassembler on the 16-bit executable, the routine responsible for port communication was located in a small, 0x90 byte code segment. While the decompiler struggled with this segment, the resulting assembly disassembly revealed the use of IN and OUT instructions for parallel port I/O operations.
The analysis showed the routine performed a series of writes and reads to the parallel port status register, ultimately storing a result in the BX register upon returning. Since the routine appeared to take no external inputs, the output value was determined to be constant, regardless of the dongle’s presence.
The strategy shifted to patching the routine’s entry point to force an immediate return with a predetermined value in BX. Early patching confirmed that the routine always set the high byte of BX (BH) to 76h, leaving only the low byte (BL) as the unknown variable.
By scripting an automated brute-force attack using DosBox to test all 256 possible values for BL, the correct authentication sequence was identified. The required magic number for the BX register was determined to be 7606h, allowing the compiler to execute without the physical hardware attached.