Resolv Digital Assets suffered a major security breach on Sunday morning, causing its USR stablecoin to lose most of its value. An attacker exploited a contract vulnerability to mint unbacked tokens worth approximately $80 million around 2:21 a.m. UTC. The incident has sent shockwaves through the decentralized finance community regarding protocol safety and smart contract auditing standards.
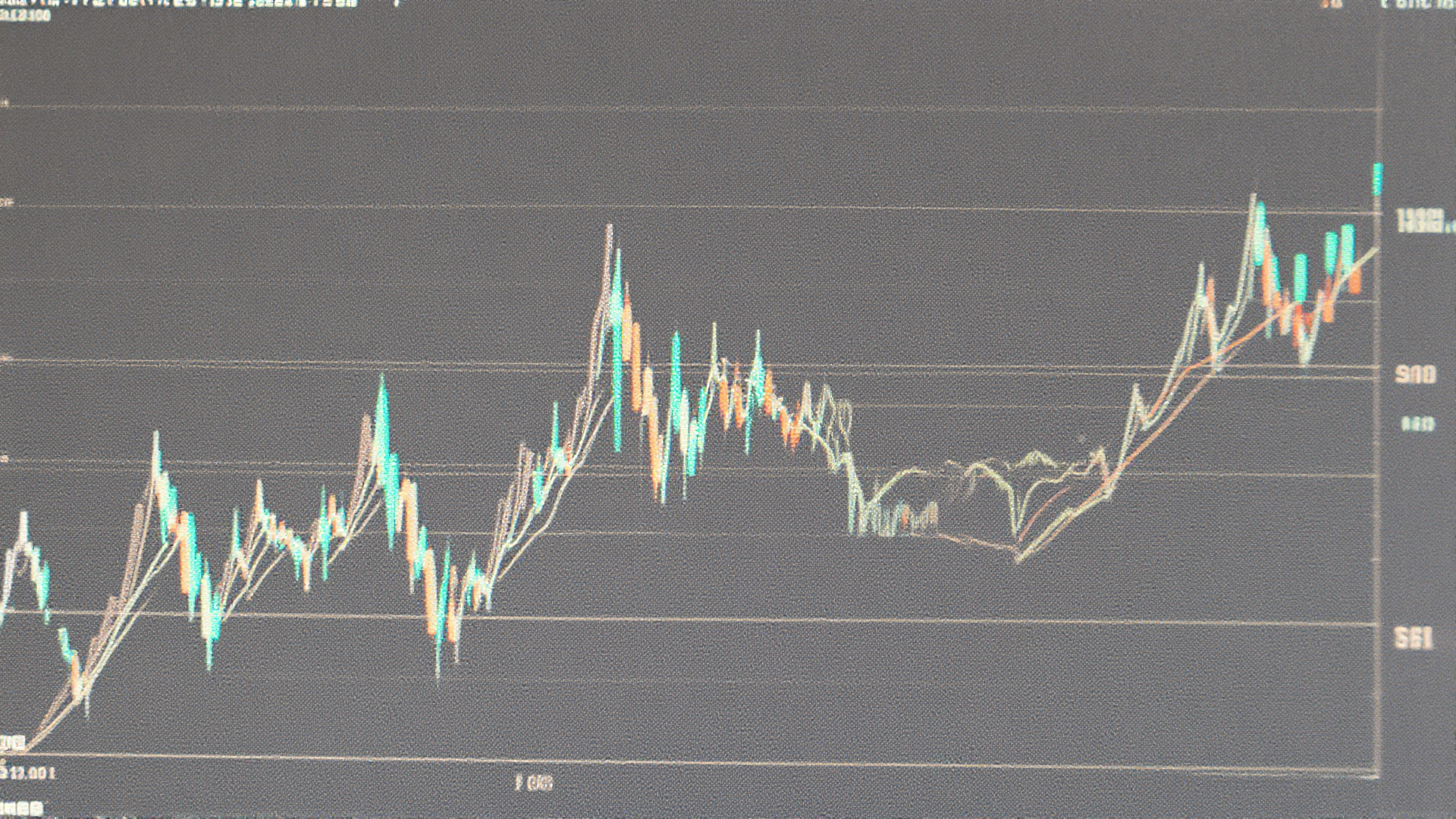
Immediate market reaction saw USR plummet from its dollar peg to $0.025 on Curve Finance within 17 minutes of the first transaction. Although the price briefly recovered to $0.85, trading data shows it currently sits at $0.27. This represents a 72% decline over the course of the week, rendering the peg ineffective for users. DEX Screener data confirms the speed of the price collapse across liquidity pools. The rapid depegging signals a loss of confidence among immediate traders and liquidity providers.
Blockchain analysis indicates the attacker swapped the minted tokens for USDC and USDT across multiple decentralized exchanges. They subsequently converted the proceeds into Ethereum, holding 11,409 ETH worth roughly $23.7 million in a specific wallet. Another address reportedly retains $1.1 million in wrapped USR, complicating asset tracing efforts. The funds were moved quickly to obscure the transaction trail and prevent immediate freezing. This speed highlights the efficiency of modern crypto mixing and swapping tools.
Resolv initially attributed the breach to a compromised private key and targeted infrastructure attack in their public statement. However, onchain investigators revealed the root cause was a structural design flaw within the minting contract itself. The SERVICE_ROLE account was controlled by a single externally owned account instead of a secure multisig arrangement. This distinction is critical because a single key compromise differs from a systemic contract vulnerability. The team must now address the underlying code architecture rather than just key management.
Critical safety mechanisms were missing from the protocol, including real-time oracle checks and maximum mint limits. The system allowed a deposit of 100,000 USDC to yield 50 million USR without any mathematical validation. This ratio was roughly 500 times higher than what the protocol intended for stablecoin minting, exposing a massive logic gap. The lack of validation meant the contract accepted any deposit ratio without questioning the mathematical impossibility. Consequently, the attacker deposited 100,000 USDC and received 50 million USR in return, bypassing standard risk controls entirely.
Ido Sofer, founder of crypto key management firm Sodot, noted that such setups are not unusual but create significant vulnerabilities. He stated that sensitive keys often overlooked by security teams serve as single points of failure for internal and external threats. This trend highlights risks in credentials that do not hold funds directly but grant access to them. Security audits must now prioritize permission structures over simple access control lists. Developers should implement stricter governance models to prevent future exploits.
DeFiLlama data shows the protocol's total value locked peaked near $684 million in February 2025 before the market cooled. TVL declined significantly to around $95 million before the exploit occurred on March 23, indicating waning confidence. This financial contraction suggests the project struggled to maintain liquidity prior to the security incident. The decline reflects broader market uncertainty affecting the entire DeFi sector. Investors withdrew capital as the project faced liquidity challenges before the attack.
The team announced they are working with law enforcement and analytics firms to recover assets from the attacker. They advised users against trading USR while recovery measures are being implemented across the ecosystem. Actions taken by users during this period may affect the overall recovery strategy and token value. The company emphasized that transparency is key to rebuilding trust in the aftermath of the breach. They will provide updates as their legal efforts progress.
The event raises questions about delta-neutral hedging strategies backed by ETH and BTC on decentralized platforms. Investors are scrutinizing how protocols manage collateral and minting permissions during high volatility periods. Trust in algorithmic stability mechanisms faces renewed pressure from this latest failure. Investors are now questioning the efficacy of delta-neutral strategies that rely on complex hedging to maintain the peg. This incident underscores the fragility of algorithmic models when core permissions are not tightly restricted.
Industry observers will watch closely for any successful asset recovery efforts in the coming weeks. Future audits and regulatory inquiries may follow this high-profile exploit within the broader crypto sector. Security firms will likely increase their scrutiny on single-signature roles in critical DeFi infrastructure. Developers must now prioritize security audits before deploying new smart contracts. The event serves as a cautionary tale for the next generation of decentralized finance applications.